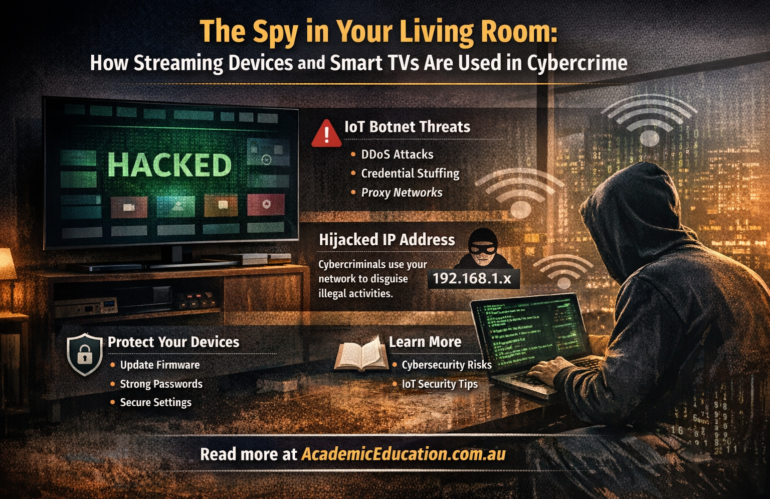
Smart TVs, streaming boxes, and other connected home devices are now a standard part of everyday life. However, recent cybersecurity research shows that these devices are increasingly being targeted and exploited by cybercriminals. A large-scale operation known as KimWolf botnet demonstrates how vulnerable Internet of Things (IoT) devices can be when security is overlooked.
What is the KimWolf botnet and how does it work?
The KimWolf botnet infected more than two million Android-based devices globally, including smart TVs, streaming devices, and other IoT hardware. Attackers exploited software vulnerabilities to gain control of these devices without the user’s knowledge.
Once compromised, the devices were turned into proxy servers, allowing cybercriminals to route internet traffic through the victim’s home network. This means malicious activity appeared to come from legitimate residential IP addresses, making detection much harder.
Why cybercriminals target streaming devices and smart home technology
Unlike traditional computers, many IoT devices:
- receive fewer security updates
- have weak default configurations
- are rarely monitored by users
This makes them ideal targets for large-scale attacks. In the KimWolf case, infected devices were used for:
- Distributed Denial-of-Service (DDoS) attacks
- Credential stuffing attacks using stolen passwords
- Proxy monetisation, where attackers sell access to residential IP addresses
Over a short period, the botnet issued billions of commands, highlighting the scale and automation of modern cybercrime.
How hackers make money from your home network
One of the most important aspects of this attack is its business model. Cybercriminals installed software that allowed them to sell access to infected devices through commercial proxy networks.
In simple terms, your home internet connection could be used to:
- bypass geographic restrictions
- hide illegal activity
- run automated attacks
All without your knowledge.
Risks for everyday users
The impact goes beyond slower internet speeds. If your device is compromised:
- Your IP address may be linked to illegal activity
- Your network security is weakened
- Other devices in your home could be exposed
Because the traffic appears legitimate, it can be difficult for law enforcement and cybersecurity systems to distinguish between normal and malicious behaviour.
How to protect your smart TV and streaming devices
To reduce the risk of IoT-based attacks, cybersecurity experts recommend:
- Keeping device software and firmware up to date
- Buying devices from reputable manufacturers
- Changing default usernames and passwords
- Disabling unnecessary remote access features
- Using network segmentation in home and business environments
Taking these steps can significantly reduce the risk that your devices will be used in a botnet.